What Can DDoS Attacks Mean for Black Friday and Cyber Monday?
This weekend's huge number of online shoppers could result in an influx of cyber crime. Two experts discuss how DDoS attacks can affect retailers and how marketers can prevent them.
This weekend's huge number of online shoppers could result in an influx of cyber crime. Two experts discuss how DDoS attacks can affect retailers and how marketers can prevent them.
Online shopping is at an all-time high, with retailers expected to rake in more than $6.5 billion in revenue this weekend, the busiest of the year. But with all those people shopping, it’ll also be a busy weekend for the people who administer distributed denial-of-service (DDoS) attacks.
“You can almost think of [DDoS attackers] as pirates,” explains Lisa Joy Rosner, chief marketing officer at Neustar, an information services and analytics company headquartered outside Washington. “What they do is they create this fake overload on your system and stuff all this fake traffic on your site.”
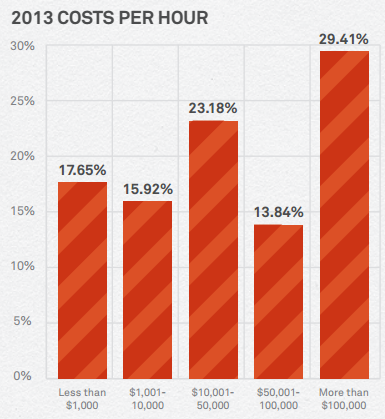
Whether DDoS attacks are designed to get a ransom from site owners (“pay up and we’ll stop”) or create a diversion, allowing hackers to sneak in and install data-stealing malware while the attention is on the attack, they rose 71 percent from 2012 to 2013, according to Neustar’s annual impact report. More than 40 percent of the study’s respondents report losses of at least $1 million per day while their sites were slowed down.
DDoS attacks don’t only hurt brands financially. It only takes a quarter of a second to lose a customer and not much longer for people to flood the call centers. Unable to handle the volume of customer complaints, companies experience decreased brand confidence as a result.
“When marketers make checklists of how to make it through the holidays, they have to think about everything, including the safety of the site and the contribution that makes to the customer experience,” says Rosner, who referred to DDoS attacks as digital armed robbery.
Though 95 percent of companies have some form of DDoS protection, it’s not necessarily the right kind. Firewalls, routers, and intrusion prevention systems aren’t designed for attacks, and can ultimately accelerate outages by bottlenecking traffic.
“Every connection, whether legitimate or not, will utilize a link in their cable, using memory in the firewall,” says Frank Ip, vice president of marketing and business development at Black Lotus, a San Francisco DDoS-mitigation service. “That eventually overwhelms the stability, so firewall is not a solution.”
Ip says that botnets, or compromised Internet connections, are especially prevalent in India, Indonesia, and Vietnam, countries with huge populations of young mobile users who predominantly use Androids, which are more easily corruptible than iOS. Mobile users are more susceptible to unwittingly committing cybercrime because of free Wi-Fi that lacks encryption, though Ip points out that large retailers are generally too savvy for their websites to be similarly unprotected.
“It’s the same protocol,” Rosner agrees. “They’re designed to go across devices, whether it’s a laptop or an iPhone or an iPad or Android or what have you. The same security is embedded across all different types of channels.”
For marketers to protect their websites, it can be as simple as having equipment to deal with an attack or working with a third-party mitigator who does. Rosner says that it’s important to have an early-warning system to detect anomalies, such as a sudden influx of traffic from another country.
Ip adds, “If you compare the intangible losses – customer goodwill, brand equity – it will be a small amount of money to put some preventative resources in place.”
Homepage image via Shutterstock.
Leave a Reply
You must be logged in to post a comment.